J'aime bien les nuages quand il y a du soleil derrière.
#photography #cloud #nuage #pictorialisme
J'aime bien les nuages quand il y a du soleil derrière.
#photography #cloud #nuage #pictorialisme
J'aime bien les nuages quand il y a du soleil derrière.
#photography #cloud #nuage #pictorialisme
J'aime bien les nuages quand il y a du soleil derrière.
#photography #cloud #nuage #pictorialisme
Far ..
.
.
#photography
#landscape
#mountain
#color #blackandwhite
#ladder #light
#dark #mood
#sky #cloud
Far ..
.
.
#photography
#landscape
#mountain
#color #blackandwhite
#ladder #light
#dark #mood
#sky #cloud
Google #Cloud admins… has anyone found a decent method of getting automated CUD expiration notifications? At this point the best options seems to be a calendar reminder.
Chile enacted Law No. 21.719 in December 2024, replacing its 1999 privacy framework.
The law becomes fully effective on December 1, 2026.
For SaaS and cloud companies, cross-border data transfers and processor accountability are central compliance issues.
If Chilean user data is hosted outside Chile, architecture and contracts should be reviewed.
Chile enacted Law No. 21.719 in December 2024, replacing its 1999 privacy framework.
The law becomes fully effective on December 1, 2026.
For SaaS and cloud companies, cross-border data transfers and processor accountability are central compliance issues.
If Chilean user data is hosted outside Chile, architecture and contracts should be reviewed.
Google #Cloud admins… has anyone found a decent method of getting automated CUD expiration notifications? At this point the best options seems to be a calendar reminder.
If you care about the hardware behind LLMs, agents, and frontier AI research, Huawei’s Atlas 950 SuperPoD is worth a closer look.
#ArtificialIntelligence #Huawei #Ascend #Cloud #SuperComputing
If you care about the hardware behind LLMs, agents, and frontier AI research, Huawei’s Atlas 950 SuperPoD is worth a closer look.
#ArtificialIntelligence #Huawei #Ascend #Cloud #SuperComputing
Moving away from hyperscalers seems to be a growing trend.
The reason? One respondent didn’t beat about the bush: “The risk of Trump”.
#technews #soverignty #cloud #sovereigncloud #microsoft #aws #oracle #sap
Moving away from hyperscalers seems to be a growing trend.
The reason? One respondent didn’t beat about the bush: “The risk of Trump”.
#technews #soverignty #cloud #sovereigncloud #microsoft #aws #oracle #sap
#photography #nightphotograpy #cloudphotography
March 4, 2026 at 02:00PM
via Instagram https://instagr.am/p/DVdqIJzj38n/
#photography #nightphotograpy #cloudphotography
March 4, 2026 at 02:00PM
via Instagram https://instagr.am/p/DVdqIJzj38n/
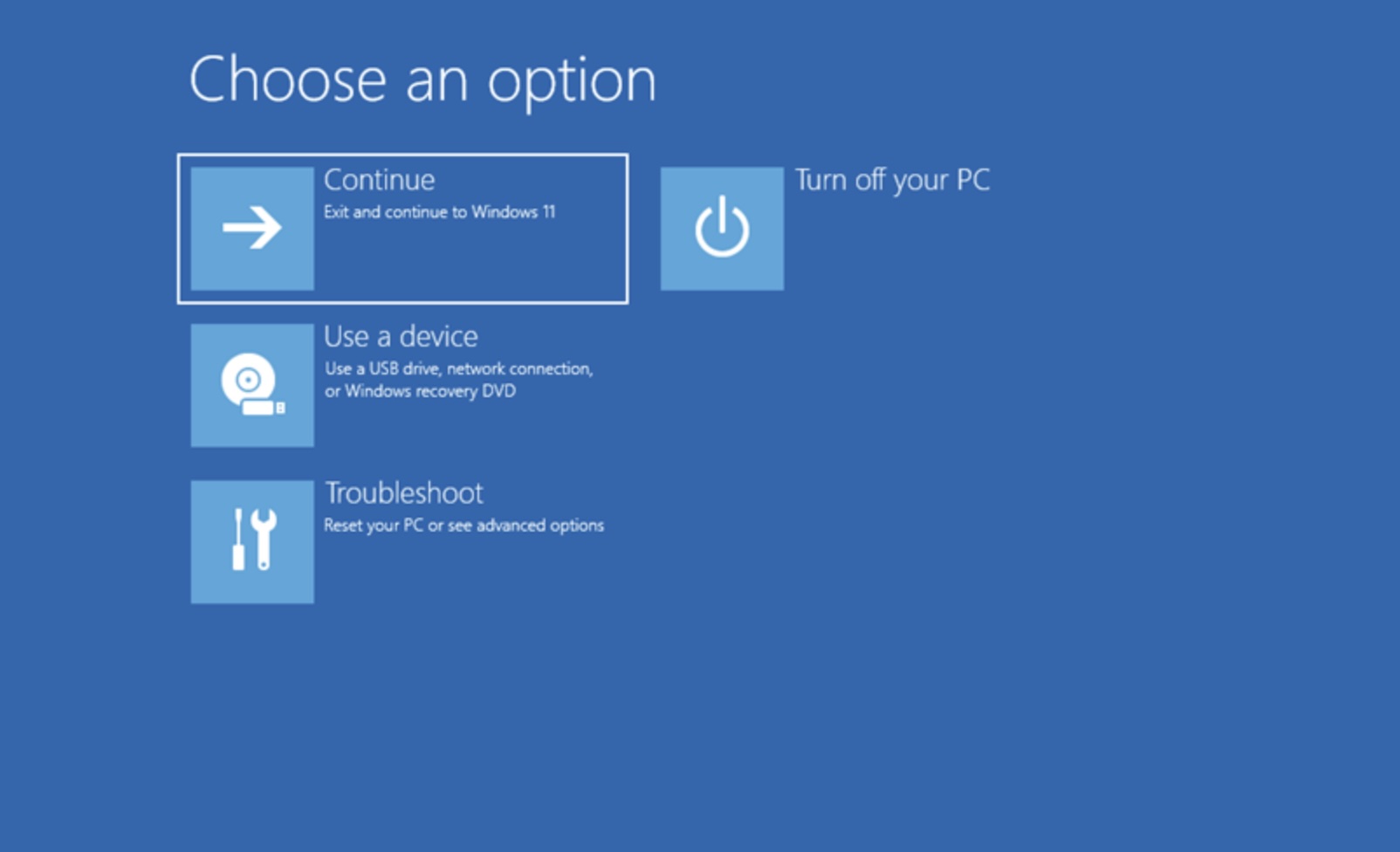
A security researcher demonstrated BitLocker encryption can be bypassed in under a minute using a Raspberry Pi Pico. By attaching a cheap microcontroller to the motherboard, he was able to sniff the encryption keys as they traveled between the CPU and the Trusted Platform Module. This attack proves that software-level security is often only as strong as the hardware bus it relies on.
The vulnerability exists because many laptops don’t encrypt the communication channel between these two critical components. When you boot your machine, the key moves in plain text across the circuit board. If a thief has physical possession of your device, they can extract your data without ever knowing your password. This serves as a reminder that full-disk encryption provides a false sense of security if the hardware design remains open to simple sniffing tools.
🧠 The bypass uses a $5 microcontroller to capture encryption keys.
⚡ Sniffing occurs during the boot sequence before the OS loads.
🎓 Only hardware with encrypted TPM buses can mitigate this risk.
🔍 BitLocker remains vulnerable on millions of existing enterprise laptops.
https://www.itnews.com.au/news/researcher-shows-physical-attack-bypassing-bitlocker-623815
#Cybersecurity #DataPrivacy #Windows #HardwareHacking #security #privacy #cloud #infosec
A security researcher demonstrated BitLocker encryption can be bypassed in under a minute using a Raspberry Pi Pico. By attaching a cheap microcontroller to the motherboard, he was able to sniff the encryption keys as they traveled between the CPU and the Trusted Platform Module. This attack proves that software-level security is often only as strong as the hardware bus it relies on.
The vulnerability exists because many laptops don’t encrypt the communication channel between these two critical components. When you boot your machine, the key moves in plain text across the circuit board. If a thief has physical possession of your device, they can extract your data without ever knowing your password. This serves as a reminder that full-disk encryption provides a false sense of security if the hardware design remains open to simple sniffing tools.
🧠 The bypass uses a $5 microcontroller to capture encryption keys.
⚡ Sniffing occurs during the boot sequence before the OS loads.
🎓 Only hardware with encrypted TPM buses can mitigate this risk.
🔍 BitLocker remains vulnerable on millions of existing enterprise laptops.
https://www.itnews.com.au/news/researcher-shows-physical-attack-bypassing-bitlocker-623815
#Cybersecurity #DataPrivacy #Windows #HardwareHacking #security #privacy #cloud #infosec